The past few years have proven that the flexibility of hybrid and remote work environments improves work-life balance, decreases stress and increases employees’ overall satisfaction. But these environments also create unique security and privacy challenges. An IBM report shows the average data breach in 2022 cost a cool 4.35 million, a 12.7% increase from 2020. Stolen or compromised credentials were responsible for 19% of breaches, phishing for 16% of breaches and cloud misconfiguration for 15% of breaches.
At Slack, we believe your digital HQ should be a secure place to collaborate and drive work forward, where you never have to compromise anything, especially security. That’s why customers rely on our tried-and-tested security features, including enterprise-grade data protection, identity and device management, and information governance.
This September, Slack is releasing audit log UI, the third of three new security features for enterprise customers that enhance Slack’s already robust security program. “Slack’s mission is to make people’s working lives simpler, more pleasant and more productive, and a big part of that is ensuring we keep data secure,” says Slack’s vice president of security, Kevin Clark. Together, with the already released session anomaly events and multi-SAML login feature, these new tools make for a broad security update that will help teams protect themselves from external and internal threats without any extra budget, head count or code needed.
“Regardless of the size, industry or line of business, security should always be top of mind for an organization, particularly in the new dynamic work landscape,” says Eric Karlinsky, group product manager on Okta’s Zero Trust team. “Defending against modern attacks requires active participation from all technology vendors, and we must adopt a shared-fate mindset with our customers. We are very excited that Slack is detecting anomalous events, investing in security tools and partnering with Okta to help companies become more secure against evolving threats.”
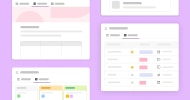
Detect suspicious behavior and take action with a no-code audit log
To help organizations easily detect suspicious behaviors and take immediate action, a new audit log dashboard allows admins to swiftly review relevant events. Previously only available via API, this no-code UI is especially helpful for companies without the budget or head count for continuous auditing or expensive SIEM tools.
Let’s say a user’s stolen or reused password compromises their Slack account and your admin would like to see which public channels were previewed by the attacker. Instead of manually digging around for more information—a time-consuming process that distracts from daily work—the log automatically flags activity for your internal team to review further. Using the dashboard, you can search for the attacker and our new event “public_channel_preview” to see all channels the user previewed. You’ll also have the ability to allocate permission to admins, giving them access at an organizational level.
Launching in September, this feature will seamlessly increase your admin’s bandwidth and alleviate frustration, saving time and money that might otherwise go toward expensive audits or potential fraud.

“Protecting our customers at every layer is one of our most important responsibilities, so we’ve built an industry-leading security program based on the concept of defense in depth.”
Protect your Slack instance with proactive alerts
To keep your digital HQ safer and more secure, session anomaly events allow Slack to flag irregular activity to your company’s audit logs so that you can perform your own internal reviews as needed. We automatically analyze Slack sessions to surface potentially harmful inconsistencies, such as session-switching networks or cloning fingerprints from a token. These events are added to your audit logs, which are viewable via the API or UI.
To help prevent unwanted activity and aid in facilitating your security team’s discovery of and investigations into anomalous use of your Slack instance, we’ll be adding additional anomaly events to the audit logs over the coming quarters.
“We’re committed to continuing to deliver security features like these because we believe access to new capabilities and data levels up our customers’ security posture, and the rising tide lifts all boats. We’re all in this together.”
Configure 12 different identity providers to a single organization
For organizations that use multiple identity providers (IdPs), admins now have multi-SAML, enabling users to securely sign in to Slack from up to 12 different identity providers. Instead of requiring a subset of employees to use email and password, this option gives everyone more control and security, which is especially helpful for global organizations or those acquiring companies that use a different provider.
“These new security enhancements provide even more transparency and ease of use, so anyone—regardless of their technical background—can feel secure in this new era of work.”
A secure digital HQ where your teams do their best work
We’re committed to listening to our customers and developing tools and features that help make your work lives simpler and more productive, with intuitive and reliable security. We hope these enhancements make your everyday lives even more secure, seamless and efficient, but please continue to share any needs, ideas and inspiration you have as we shape the future of the digital HQ together.
Have questions? Learn more.